Why Is Compliance Software Important? And How Do I Know If I Need It?
Compliance officers have traditionally spent much of their time manually tracking the data they need to ensure the firm and its employees remain in…
StarCompliance values the security of your business and your data above all else. StarCompliance Enterprise is hosted in SOC 2 and/or ISO 27001 data centers that provide high availability. As an organization, StarCompliance is ISO 27001, and SOC2 Type II compliant.

The StarCompliance approach to security is based on a Governance, Risk and Compliance strategy, led and supported from the top down. Our Information Security and Data Protection team ensure strict policies and procedures are established and implemented in relation to best practice, legislative, regulatory, legal and contractual requirements. These procedures are coupled with the authority to enforce the controls – administrative, technical and physical – which protect our security principles of confidentiality, integrity and availability.
StarCompliance conforms to standards defined by the International Organization for Standardization (ISO) and is certified to:

ISO 27001 – Information Security Management System
Our systematic approach to managing sensitive company information ensures it remains secure. This involves applying robust risk management to our people, processes and IT systems.
ISO 27005 is the Risk Management Framework that underpins ISO 27001. Risks are identified internally by our Information Security and Data Protection team and externally in our annual, independent, third-party audits.
Our compliance program includes:
Star’s advanced implementation and security options ensure your compliance operations are safer and more efficient than ever before.
With STAR Mobile, employees pre-clear activity and report transactions on-the-go and Supervisors can review escalated requests from anywhere.
STAR offers a range of products, services and vendor solutions that let you monitor and manage an ever-increasing amount of data, enhance and optimize existing data sets, and maintain data integrity.
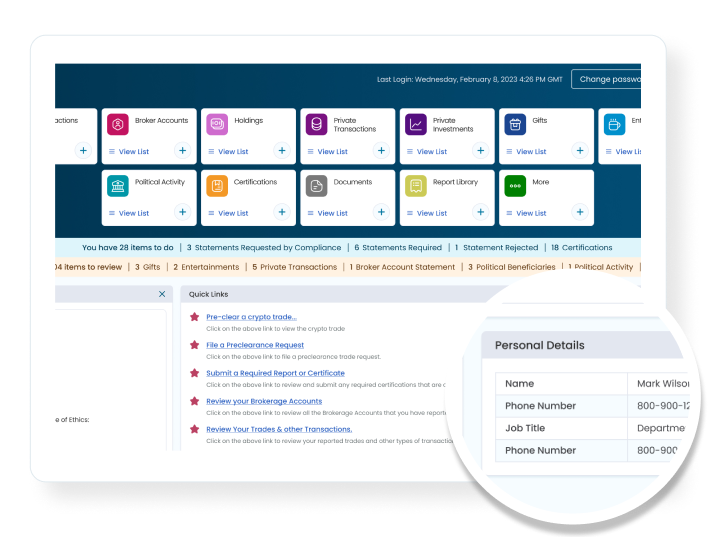
Be proactive, not reactive. Put actionable intel in front of compliance officers and frontline managers in an interactive format in near-real time.
GuideMe is your compliance software training partner. Get instant support right inside the application.
Compliance officers have traditionally spent much of their time manually tracking the data they need to ensure the firm and its employees remain in…

The journey to a new compliance system begins here, no matter where you’re starting out from

While traditionally associated with multinational corporations and financial institutions, compliance obligations are now ubiquitous, extending even to small retailers.